Zero Trust vs VPNs
Legacy solutions are increasingly becoming more obsolete with enterprise migration to the cloud and digital transformation. They are not only more vulnerable to attacks, but also don’t provide visibility and monitoring capabilities.
InstaSafe’s Zero Trust Solutions address these challenges and shield your enterprise assets from attacks from outside or inside the perimeter- by re-defining the perimeter itself

The VPN is not designed for modern enterprises
Your VPN infrastructure is not optimised for the cloud. Even though a VPN service may provide secure remote connectivity to enterprise applications, it presents several security risks that put the entire network at risk, and hamper user experience.
Management Complexity
Increased Attack Surface- Excessive network access leads to lateral movement within the network and exposes a larger vulnerable attack surface
Excessive Implicit Trust
VPNs assume excessive implicit trust to all users, allowing malicious actors to exploit your enterprise network
A more Secure VPN Alternative
Backhauling of traffic, as with VPN solutions, causes latency for distributed workforces. Experience zero latency connections with InstaSafe's Zero Trust Access solutions
Perimeter Based Security
The perimeter approach to security has been rendered obsolete due to the advent of the cloud
Bad User Experience
Backhauling of end user data traffic to datacenters impedes productivity and user experience
InstaSafe Zero Trust vs VPN
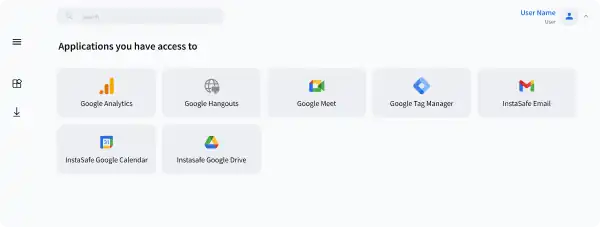
Zero Trust VPN Alternative Solutions
Least Privilege Access of our VPN replacement is based on the Need to Know Model
Separate Data and Control Planes; User data doesn't go through vendor machines
Granular, User Specific Access Policies
Our VPN Alternative offers All round visibility, and seamless integration with reporting tools
Highly Cost Effective, born in the Cloud solution
Logging of All network traffic for audit and compliance
Seamless remote connectivity to users across the world
Our alternative of VPN offers easy scalability, deployable in days
Traditional VPN Solutions
High Scope for unauthorised Access by malicious actors
In absence of zero trust VPN alternatives, all data is inspected by vendor machines, and susceptible to supply chain attacks
Unable to create custom access policies
Weak or no Monitoring and Analytics
Hardware based solutions, difficult to maintain
Network Activity and logging reports are not produced
Remote user connectivity is usually not present. When present, it is flawed and hinders user experience
Hardware based solution, not scalable on demand like VPN alternatives of InstaSafe
Benefits of Zero Trust Security
Enhanced Security
Only Authenticated Users and Authorized Devices are able to 'see' and access applications with zero trust security
Better Visibility
Gain a Bird’s eye view over all network traffic with zero trust model and identify threat vectors in real time
Simplified Access Control
Role based access to business applications on a need to know basis. One Click Access for better user experience
Simplified Deployment and Hyper scalability
Hardware Free. Rapidly deployable, scale as you go solutions
What features of the InstaSafe Zero Trust approach stand out when compared to VPNs?
Granular Access Control
Control who accesses which resource, where, from which device, and at what time, all with a single solution
Privacy First
Ensure data privacy by restricting enterprise data flow through vendor machines
Tunnelled Application Access
Authorised users get access only to authorised applications and nothing else
Server Blackening
Reduce your exploitable attack surface by making your assets completely invisible to the internet
Our Approach to Zero Trust
Moving Beyond the “Castle and Moat” Security Model to Zero Trust Security
Authentication Before Access
Combine seamless integration with IDP and AD, with integrated MFA and SSO capabilities to ensure secure and seamless one click access to applications
Know Morearrow_forwardGranular Access Controls
Set up access controls for applications, file and service access
Know Morearrow_forwardContinuous monitoring of Network & device behaviour
Get 360 degree visibility with easy integration with SIEM Tools
Know Morearrow_forwardThreat Intelligence and Alerts
Detect security events like invalid login attempts, bruteforce attacks; Check health of gateways and devices and provide alerts
Know Morearrow_forwardWant to learn more on the difference between Zero Trust Network vs VPN and know how InstaSafe compares against legacy solutions?