Securely Access your Web Applications with Clientless Remote Access
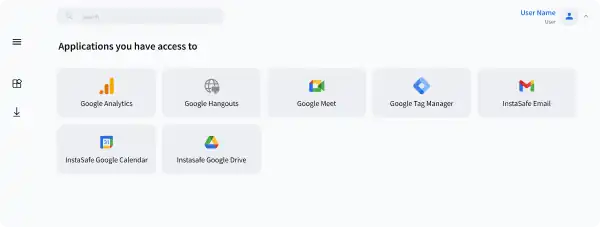
With our Clientless remote access, you can directly access any web- based application using a web browser access portal. No Client to install. Agnostic of any Operation System and any Browser
Why does your organization need Clientless Remote Access?
Managing Access of Third Party Partners
Enable secure access to specific applications for third party users without the need to manage their device.
Eliminating Interoperability Issues
Ensuring client works for all OS and device type can be cumbersome. Clientless remote access is hassle free
Restricted Access
Access to specific applications and resources on a "Need to know basis", without compromising security
Features of Clientless Remote Access includes
Detailed Audit Logs
Flexible Usage
Simplified Management
Seamless User Experience
Benefits of Clientless Remote Access
Simplified User Access
Prevent lateral movement, and extend security to your cloud assets and remote workforces with confidence
Secure Third Party Access
With our Alternative of VPN, you get Seamless, Secure Single Click access to all applications hosted anywhere, with no backhauling and no latency
Enhanced Security
Remove redundant VPN based security stacks requiring complex management with a single unified secure access solution
Better Access Controls
Make sure that your user traffic is accessible only to you, with the Privacy FIrst approach of our VPN Alternative
Seamless Support for your Stack
InstaSafe integrates seamlessly with every internal applications, databases, and cloud




Solve your access challenges with InstaSafe
Improve your security posture and gain better control over your network with Zero Trust
 CASE STUDY
CASE STUDYSecure Access to Office 365 Applications using InstaSafe Zero Trust
Continue Readingarrow_forward WEBINAR
WEBINAREnsuring a Secure Work From Home Environment: Remote Access Security Best Practices
Watch Nowarrow_forwardFrequently Asked Questions on Clientless Remote Access
With clientless access, you can ensure secure access of your enteprise applications by 3rd party contractors without the need for installing security agents/applications on their devices. Any request for access is automatically redirected to a secure connection after being authenticated and authorised
Clientless Remote Access helps in extending secure access beyond your workforce to your entire ecosystem, and can be used to scale up remote work capabilities quickly without facing the hassles of installing agents on user devices
With Clientless Remote Access, you can ensure ease of use for the end user, without hampering security. At the same time, security teams also have complete control and visibility over who accesses what
All HTML Web applications and SaaS apps can be accessed via clientless remote access
Zero Trust Application Access
Secure Single Click Unified Access to SSH/RDP Servers and Applications hosted anywhere, by workforces located anywhere
Zero Trust Network Access
Leverage granular access policies, passwordless authentication, and visibility across your network with the ZTNA solution
Secure Cloud Access
Empower your Remote Workforce to seamlessly connect and work securely, from Anywhere.
VoIP Access
Extend Secure Remote Communication Channels for Remote VoIP users with a Zero Trust Solution
Are you ready to be a part of the Zero Trust Secure Access Revolution?