Zero Trust Network Access
Secure your network and minimize attacks surface with our Zero Trust Network Security framework. Leverage granular access policies, password less authentication, and visibility across your network with the Zero Trust Network Access solution
With Zero Trust Network Access, create fast, encrypted connections and connect applications and servers seamlessly at the network layer
Private, Encrypted Tunnels
With Zero Trust Enterprise Network, create secure, encrypted connections from user devices to the networks they wish to access
Invisible Network
Remove exposed IPs and make your network invisible to the internet
Secure Data
All data in transit is end-to-end encrypted, and your traffic doesn't go through vendor machines
Never Trust, Always Verify
Employ a default deny for all approach, and remove excessive trust from your network with a Zero Trust Network Security model
Continuous Risk Assessment
Enable complete risk and trust assessment for every request for access continuously with zero trust network access solutions
Use Cases of Zero Trust Network Access
Secure Access to Thick Client Applications
Enable secure access to thick client applications through IP Level Access
Secure SAP Applications
Secure access to your SAP Applications by workforces situated anywhere
Secure Access to Linux Machines
Enable secure Desktop level PuTTY access to your Linux machines
Secure IP Access
Remove exposed IPs and enable secure access to devices/application servers at the IP layer with Zero Trust Network implementation
Security and Confidence for the entire organization
IT & Operations
Easy to Scale : Cloud-Delivered solution optimised to enable easy management and scalability
Easy to Configure : Seamless integration with IDPs to enable easy configuration of access policies along with Zero Trust Network implementations
Easy to Manage : Centralised Security Control from asingle dashboard
Seamless Onboarding : Deploy on end- user devices in 3 simple steps, with a choice of agent- based/agentless approach to Zero Trust Network Access

Business Leaders
Cloud Ready Solution : Future Proof your infrastructure with a cloud ready solution that was built to secure hybrid workforces and hybrid applications
Improve Security Posture : Make your assets invisible to the external internet and allow visibility only to authorized users with a Zero Trust Network Security model
Increase Business Agility : Make your IT infrastructure more responsive to business needs, and enable smooth transitions quickly and securely
End Users
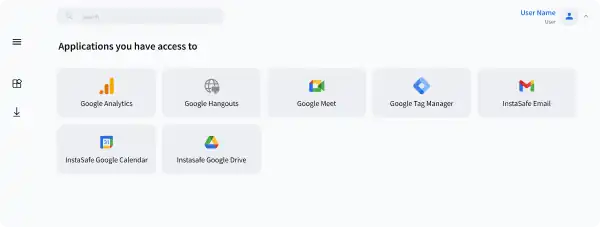
Secure, Single-Click Access to Applications : Ensure secure Zero Trust Network Access to all end user authorized applications from a single platform
Work from Anywhere : Let your workforces access your enterprise assets securely, no matter where they are.
Unhindered Connectivity : Our Zero Trust Network Security model removes the hassles of backhauled traffic, increased latency and poor user experience due to VPNs. With a single click access based platform, spend less on training and support

Benefits of Zero Trust Security
Enhanced Security
Only Authenticated Users and Authorized Devices are able to 'see' and access applications with zero trust security
Better Visibility
Gain a Bird’s eye view over all network traffic with zero trust model and identify threat vectors in real time
Simplified Access Control
Role based access to business applications on a need to know basis. One Click Access for better user experience
Simplified Deployment and Hyper scalability
Hardware Free. Rapidly deployable, scale as you go solutions
Seamless Support for your Stack
InstaSafe integrates seamlessly with every internal applications, databases, and cloud




Steps to Implement Zero Trust Network Access
Zero Trust is a journey which every organization needs to take a phased approach of Zero Trust implementation and work on continuous refinement. There is a five step process for Zero Trust Implementation.
Define your protect surface
Identify the assets which includes data, applications, cloud resources that you want to protect.
Map the transaction flows
Understand the network traffic flow among the assets that needs to be protected and the user devices.
Build a Zero Trust architecture
Based on network traffic flow, create a design that will best protect the assets. The design will determine how many gateways, placement of gateways and controller.
Create Zero Trust Policy
Implement policy in the controller on which user can access what resources and what point of time. Under what conditions, users need to be provisioned and de-provisioned
Monitor and maintain the network
Inspect all the logs related to user and network activity to have better visibility and take corrective action if required.
ZTNA vs. VPN: Understanding the Difference
Zero Trust VPN Alternative Solutions
Least Privilege Access of our VPN replacement is based on the Need to Know Model
Separate Data and Control Planes; User data doesn't go through vendor machines
Granular, User Specific Access Policies
Our VPN Alternative offers All round visibility, and seamless integration with reporting tools
Highly Cost Effective, born in the Cloud solution
Logging of All network traffic for audit and compliance
Seamless remote connectivity to users across the world
Our alternative of VPN offers easy scalability, deployable in days
Traditional VPN Solutions
High Scope for unauthorised Access by malicious actors
In absence of zero trust VPN alternatives, all data is inspected by vendor machines, and susceptible to supply chain attacks
Unable to create custom access policies
Weak or no Monitoring and Analytics
Hardware based solutions, difficult to maintain
Network Activity and logging reports are not produced
Remote user connectivity is usually not present. When present, it is flawed and hinders user experience
Hardware based solution, not scalable on demand like VPN alternatives of InstaSafe
Frequently Asked Questions on Zero Trust Network Access
As a cloud agnostic, heterogeneous solution, InstaSafe has been built with the aim of providing seamless functionalities across hybrid and disparate environments, including wired, wireless, virtualized on-premise data centers, and cloud infrastructures. InstaSafe’s solutions have been designed to operationalise Zero trust policies across all environments and provide a seamless and unified user experience across any platform being used. InstaSafe helps in the implementation of security policies defined by teams to a very large range of network infrastructure and security products
InstaSafe’s Zero Trust Solutions are in line with the Zero Trust framework from the top down. InstaSafe enables IT teams to strategically implement Zero Trust across all portions of their enterprise networks. With powerful authentication and monitoring capabilities, InstaSafe starts with full visibility for all IP-connected devices across enterprise segments, including campus, data center, cloud and operational technology (OT) environments. The Zero Trust Network Access Solution provides deep inspection of device security and configuration state to determine the device risk posture. The InstaSafe policy engine translates the enterprise’s security policies and segmentation strategy into the rules applied by individual enforcement products based on the device’s risk posture and the user identity, and on this basis they classify an access request made by a device as trusted or untrusted. Additionally, InstaSafe’s zero trust approach to network security is easily integrable with monitoring and security tools like SIEMs and SAML/ADs, to simplify security management for teams.
Zero Trust systems are essentially touted to replace traditional security setups for more than 80% enterprises by 2023. This means that organization wide Zero trust Network strategy adoption needs to be one of the top priorities for CIOs and CISOs. Since Zero Trust is meant to be less of a single point solutions, and more of a strategy, Zero Trust enabling technologies need to incorporated into every enterprise’s security stack to keep their security posture future ready
InstaSafe ZTAA is used to provide segmented application access by leveraging application specific tunneling. In essence, it provides application access without giving network access. InstaSafe Zero Trust Network Access (ZTNA), on the other hand, is used for very specific use cases that involve extending secure applications to thick client applications, and extending secure access to devices/applications at the IP layer, as opposed to access at the application layer for ZTAA.
Are you ready to be a part of the Zero Trust Secure Access Revolution?