Secure VoIP Access for Remote Users
Extend Secure Remote Communication Channels for Remote VoIP users with a Zero Trust Solution

Issues with current VoIP Solutions
With Remote Access becoming the new norm, companies using VoIP services are forced to shift to remote models, which increases security and compliance risks
Shifting to dynamic IPs poses a challenge in terms of tracing user activity
It becomes tough to ensure regulatory compliance for VoIP users
Remote connectivity extension would have network connectivity and latency issue
IP networks used for carrying voice traffic, induce latency which may result in call drops and jitters during calls
Challenges of using VPNs
Traditional Solutions are not equipped to handle secure remote access by VoIP users
Expose Internal resources to malicious actors
Do not provide advanced features like device posture checks and access control
Cannot restrict users access on the basis of their location, their time of access, and the type of device used for access
Lack of strong authentication measures and visibility over user activity

With InstaSafe, the world's largest BPMs are ensuring business continuity. Here's how
Leverage a private channel on the dynamic IP that connects to the datacenter, and a VoIP gateway that removes latency issues
All data in transit is end to end encrypted with seamless and instant military grade AE256 encryption, to improve voice quality
Ensure that your voice data is accessed by the right users with integrated MFA capabilities
Leverage additional security controls like device posture checks, geolocation, geo binding, to bind users to particular secure devices
Ensure complete visibility over user activity with activity logs
Frame customised, contextual access policies to restrict or allow access to resources
Better VoIP security for remote access through the Zero Trust approach
InstaSafe's Zero trust Solutions allows easy remote VoIP access for your workforce, while ensuring security and compliance
Better Performance
InstaSafe helps in authorised access through a VoIP gateway. All traffic is passively monitored without adversely affecting network performance.
Instant Deployment
InstaSafe can be deployed across workforce machines instantly, and can be scaled up in a matter of days
Better Security
Your voice data is not only end-to-end encrypted, but also completely inaccessible to the external internet
Simplified Access
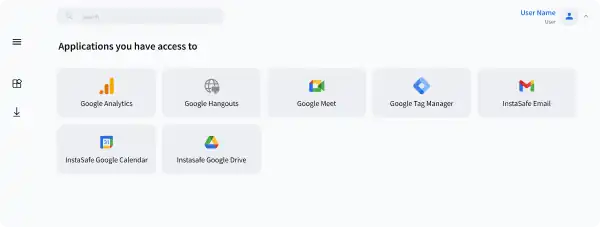
With our One Access solution, you require just one unified answer for secure VoIP access, web app access, SAP access etc
Solve your access challenges with InstaSafe
Improve your security posture and gain better control over your network with Zero Trust
 CASE STUDY
CASE STUDYSecure Access to Office 365 Applications using InstaSafe Zero Trust
Continue Readingarrow_forward WEBINAR
WEBINAREnsuring a Secure Work From Home Environment: Remote Access Security Best Practices
Watch Nowarrow_forwardWhat Our Customers Say on G2
InstaSafe acts like a natural extension to our network infrastructure.
With its clientless functionality, it works seamlessly in the background, and causes no latency issues whatsoever during usage. The additional benefits of very quick scalability and adaptability to almost any environment make InstaSafe a lucrative option

Ranjith P
Chief Manager ISG& IS Audit
Good to use, easy to manage Zero Trust VPN security tool for cloud and ERP applications
InstaSafe has been instrumental in supporting the Information Management strategy of my organization by providing a secure foundation for our hybrid network infrastructure. We have managed to easily extend always-on connectivity and secure access to our cloud and ERP applications with Instasafe Zero Trust Access. It is much faster than a VPN and much easier to manage.

Hariharan S
Vice President
Demystifying IT Security
We have been able to deploy InstaSafe’s solutions seamlessly across a diverse workforce. The interface is user friendly, which reduces the need for extensive training, and the solution is flexible in many ways, allowing for better integration with our existing infrastructure

Rishu P
Business Development Manager
Reliable, easy to set-up, and scalable solutions
InstaSafe simply stands out in terms of its dynamicity and adaptability to expanding cloud environments. I would recommend InstaSafe for any company in the retail sector.

Vaibhav S
Assistant Consultant
Best VPN solution, very quick setup & a great support team!
InstaSafe simply stands out in terms of its dynamicity and adaptability to expanding cloud environments. I would recommend InstaSafe for any company in the retail sector.

Sadanand H
VP IT Infrastructure & Governance
Frequently Asked Questions on Secure VoIP Access
The VoIP client to server communication can be taken via a secure tunnel . The access to the VoIP server will be allowed after a validation of the user through MFA and a device validation
The data traffic can reveal the critical information. Device takeover should be prevented to protect the organizations asset and misuse of it
The VoIP server is an application that listens for connections . It is not safe to expose these assets as the application can have known or unknown vulnerabilities. ZTA brings them on to a private network and securely share the access to the internet users over a secure tunnel.
- Security
- Seamless access
- User and device validation
- MFA
- IDP
- QoS
- Data taken via vendor machine ( Privacy First)
- Latency
- Disconnections
Zero Trust Application Access
Secure Single Click Unified Access to SSH/RDP Servers and Applications hosted anywhere, by workforces located anywhere
Zero Trust Network Access
Leverage granular access policies, passwordless authentication, and visibility across your network with the ZTNA solution
Secure Cloud Access
Empower your Remote Workforce to seamlessly connect and work securely, from Anywhere.
VoIP Access
Extend Secure Remote Communication Channels for Remote VoIP users with a Zero Trust Solution
Are you ready to be a part of the Zero Trust Secure Access Revolution?