Allow only devices that comply with your corporate security policies
Empower your IT administrators to take control of your corporate devices comply with predefined security policies to access enterprise applications

What is wrong with other free browsers?
Not for Enterprises
Free browsers are not built for enterprise users. There are not built keep security aspects in mind
Pop Up Ads and Redirects
Threat actors can force user redirect to malicious page with forced popup
Plugin Vulnerabilities
Vulnerable plugins can monitor user browser activity and can steal user credentials data
Weak Protection
Infected browser can steal password information and browser history data
Steps to Enable Device Posture Check
Set Rules for Device Authorization
Identify the list of posture attributes that you want to configure from 10+ available security postures. Add record value for each dataset linked to the posture variable.
AntiVirus Enabled Name, AntiVirus Installed Name, AntiVirus Updated Name, Mac Address, OS Build Version, OS Family, OS Major Version, OS Minor Version, System Domain Name, System MacAddress, System Serial number.

Apply Device posture profile in Access Policy
Apply rules for combination of posture attributes that you need to configure as per corporate device policy. Create boolean combination of rules ( And / OR) to manage any configuration.

Benefits of Device Posture Check
Allow only Trusted Devices
Provide access to devices that you trust. Allow company owned devices that meet company security policies.
Better Security Controls
Get notifications when any device deviates from predefined security policies.
Meet Compliance
Allow access for devices that meets compliance and enforce compliance on all devices
Better Device Management
Allow/ Block one or more devices based on company rules and security requirements
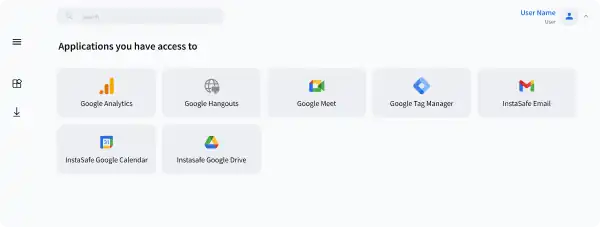
Seamless Support for your Stack
InstaSafe integrates seamlessly with every internal applications, databases, and cloud




Frequently Asked Questions on Device Posture Check
Device posture check ensures various device parameters are checked from a security perspective before allowing devices to access applications. It also ensures that devices meet security requirements of the enterprises before access is authorized.
InstaSafe Zero Trust agent can extract more than 10+ parameters from devices that can be verified. List of device parameters include AntiVirus Enabled Name, AntiVirus Installed Name, AntiVirus Updated Name, Mac Address, OS Build Version, OS Family, OS Major Version, OS Minor Version, System Domain Name, System MacAddress, System Serial number.
Administration can create boolean combinations of rules (And / OR) based on corporate rules.
Yes, it is possible to create specific rules for different user groups and separate applications, servers.
Zero Trust Application Access
Secure Single Click Unified Access to SSH/RDP Servers and Applications hosted anywhere, by workforces located anywhere
Zero Trust Network Access
Leverage granular access policies, passwordless authentication, and visibility across your network with the ZTNA solution
Secure Cloud Access
Empower your Remote Workforce to seamlessly connect and work securely, from Anywhere.
VoIP Access
Extend Secure Remote Communication Channels for Remote VoIP users with a Zero Trust Solution
Are you ready to be a part of the Zero Trust Secure Access Revolution?