Secure Remote Access Enables You to Work from Anywhere
Empower Your Remote Workforce with Secure Remote Access Solutions to seamlessly connect and work securely, from Anywhere. Make your organization future ready
Securing Remote Connections for the New Normal
Using InstaSafe's Zero Trust Remote Access solutions, your IT teams can enable, manage, and monitor access for your workforces and your applications, no matter where they are, all from a single dashboard. By allowing segmented least privilege access, InstaSafe enables your employees to seamlessly use enterprise resources without compromising your network
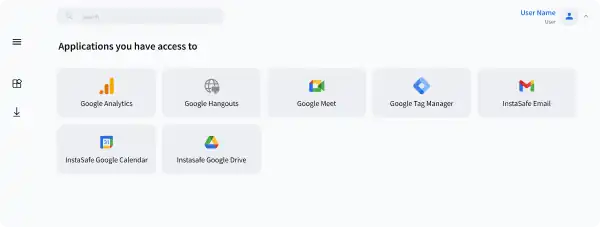
One Click Application Access
Manage access permissions, monitor network activity, conduct host and identity checks for all users and all applications from a single dashboard with our zero trust remote access solutions.
Always On Connectivity
Ensure always on secure connectivity without continuous user interaction, with automatic enablement and establishment of secure remote connections
Privacy First
Authenticate user identity and establish secure remote connections without driving any customer data through our machines, ensuring a seamless security experience
Least Privilege Access
Leverage Granular Access Control and Role Based Access Policies with our secure remote access solution to grant users the minimum access necessary to do their jobs
With Work from Anywhere becoming the new reality, Zero Trust Remote Access can enable
Secure Remote Access
For enabling secure remote access to employees working from home, companies are moving from VPNs to scalable, secure solutions like InstaSafe
Access Remote Collaboration Applications
Improve workforce productivity with fast, direct, and secure remote access to all collaboration apps from a single dashboard
Secure Web, SSH and RDP Access
Enable secure remote access solutions to Web, SSH, and RDP servers by remote workforces
Secure BYOD Access
Enable security controls for BYOD Devices and grant authorised, least privilege access with secure remote access solutions.
Secure 3rd Party Access
Secure remote connections and provide need to know access to 3rd party vendors and contractors without giving excessive network access
Benefits of Secure Remote Access
Cloud Native Secure Remote Access Solution
Cloud Native Secure Remote Access Solution
Cloud Native Secure Remote Access Solution
Cloud Native Secure Remote Access Solution
Cloud Native Secure Remote Access Solution
Cloud Native Secure Remote Access Solution
The InstaSafe Zero Trust Security Suite is a born in the cloud product that unifies least privilege access needs for data, servers, applications, and other network resources across multiple environments into a single secure remote access solution. It provides secure access to on-premises and cloud-based applications, user authentication, and data encryption to ensure that only authorized users can access corporate resources.
Solve your access challenges with InstaSafe
Improve your security posture and gain better control over your network with Zero Trust
 CASE STUDY
CASE STUDYSecure Access to Office 365 Applications using InstaSafe Zero Trust
Continue Readingarrow_forward WEBINAR
WEBINAREnsuring a Secure Work From Home Environment: Remote Access Security Best Practices
Watch Nowarrow_forwardWhat Our Customers Say on G2
InstaSafe acts like a natural extension to our network infrastructure.
With its clientless functionality, it works seamlessly in the background, and causes no latency issues whatsoever during usage. The additional benefits of very quick scalability and adaptability to almost any environment make InstaSafe a lucrative option

Ranjith P
Chief Manager ISG& IS Audit
Good to use, easy to manage Zero Trust VPN security tool for cloud and ERP applications
InstaSafe has been instrumental in supporting the Information Management strategy of my organization by providing a secure foundation for our hybrid network infrastructure. We have managed to easily extend always-on connectivity and secure access to our cloud and ERP applications with Instasafe Zero Trust Access. It is much faster than a VPN and much easier to manage.

Hariharan S
Vice President
Demystifying IT Security
We have been able to deploy InstaSafe’s solutions seamlessly across a diverse workforce. The interface is user friendly, which reduces the need for extensive training, and the solution is flexible in many ways, allowing for better integration with our existing infrastructure

Rishu P
Business Development Manager
Reliable, easy to set-up, and scalable solutions
InstaSafe simply stands out in terms of its dynamicity and adaptability to expanding cloud environments. I would recommend InstaSafe for any company in the retail sector.

Vaibhav S
Assistant Consultant
Best VPN solution, very quick setup & a great support team!
InstaSafe simply stands out in terms of its dynamicity and adaptability to expanding cloud environments. I would recommend InstaSafe for any company in the retail sector.

Sadanand H
VP IT Infrastructure & Governance
Frequently Asked Questions on Secure Remote Access
Secure remote access provides a number of benefits, including increased security, improved mobility, and cost savings associated with reduced travel and on-site visits. It also makes it easier for users to collaborate across multiple locations, as well as access files and applications from any location.
Some common methods for secure remote access include Virtual Private Network (VPN), Remote Desktop Protocol (RDP), Secure Shell (SSH), and Remote Authentication Dial-In User Service (RADIUS).
With the rise in remote work, companies need to extend secure access of their critical data and applications to their workforces working in their homes. Such access presents several security challenges which traditional security solutions may not be able to address. The need of the hour is a secure remote access solution that focuses on ensuring secure access from anywhere, while being scalable on-demand, and addressing the issues with traditional solutions
Traditionally, VPNs are used for extending access from the enterprise network to the user device. This is done by extending a private encrypted tunnel based connection through the internet, from the device to the network, which prevents unauthorised users from accessing the network
With the increase in unmanaged devices and workforces working remotely, VPNs have become unreliable as a remote access solution. In such a scenario, companies are moving to a Zero Trust Model, which follows the Never Trust, Always verify model, leveraging a system of continuous authentication, authorization, and monitoring to secure remote access
VPNs assume unfettered trust for a user/device once they get access to the network. This means that a compromised device can gain access to the entire network, and exploit critical information. In addition, VPNs backhaul traffic through multiple hubs, causig latency and user experience issues for the end user. In addition, VPNs do not provide the required visibility that security teams may need to ensure complete control over remote connectivity. Hence secure remote access solutions for your organization are important.
Using enterprise devices remotely and on unsecured networks, without any security controls, may lead to identity or credentials theft, and lead to a user becoming an unwitting accomplice in cyber crime. This is why it is important to use zero trust secure remote access solutions for your organization.
Not only does a Zero Trust Model employ a system of continuous authentication and authorization, it also allows access on a need to know basis. Even authorised users can access only what they are allowed to use,, and everything else is completely off limits. Resultantly, Zero Trust based remote access solutions prevent any scope for lateral movement of malicious actors within the network
While VPNs allow for remote access to be extended from an enterprise network to a remote device, they are not built for large unprecedented remote workforces that we are witnessing today. As such, scalability becomes an issue, and security challenges crop up as well
The InstaSafe Zero Trust Model employs a system of continuous authentication, authorization, and monitoring and visibility. Even authorised users can access only what they are allowed to use, and everything else is completely off limits. Resultantly, Zero Trust based remote access solutions prevent any scope for lateral movement of malicious actors within the network
Zero Trust Application Access
Secure Single Click Unified Access to SSH/RDP Servers and Applications hosted anywhere, by workforces located anywhere
Zero Trust Network Access
Leverage granular access policies, passwordless authentication, and visibility across your network with the ZTNA solution
Secure Cloud Access
Empower your Remote Workforce to seamlessly connect and work securely, from Anywhere.
VoIP Access
Extend Secure Remote Communication Channels for Remote VoIP users with a Zero Trust Solution
Are you ready to be a part of the Zero Trust Secure Access Revolution?