What are VPN Tunnels and How to Establish Security Beyond Them?
Virtual Private Networks (VPNs) have been around for quite a while now, and organisations have increasingly used them to secure their network infrastructure and sensitive applications against cyber security threats and online attacks.
Organisations significantly adopted VPN solutions in 2020 during the onset of the pandemic—being an easy and well-known network security solution. In fact, Atlas VPN’s VPN adoption index suggests that VPNs touched up to 277 million downloads in 2020 across 85 different selected countries.
However, despite their ease of use and simplicity, VPNs pose major security threats and challenges to enterprise networks.
This article will show what a VPN tunnel is, the problem with VPNs, and how you can establish security with excellent VPN alternatives.
What is a VPN Tunnel?
Before understanding VPN tunnels, let’s first get a gist of what VPNs are.
VPNs are network connection solutions that add security and privacy to the data transmitted between two different systems. They encrypt and encapsulate data based on the transmission protocol’s algorithm.
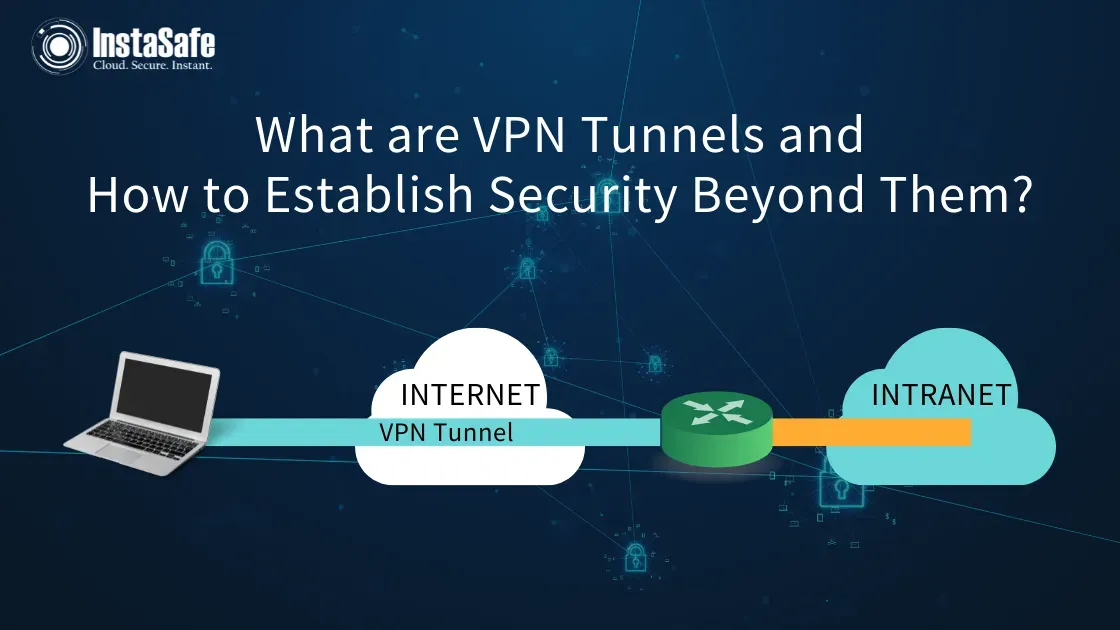
So, in essence, a VPN tunnel is the actual connection link between these two devices. It’s nothing but an encrypted connection between a VPN Server and your device that’s uncrackable without a cryptographic key—protecting users from security attacks and hiding their online activity.
You can find several types of VPN tunnels—including OpenVPN, WireGuard, SSTP, PPTP, and more.
However, even though a VPN tunnel encrypts your network traffic, hides your IP addresses, and ensures a secure connection over public Wi-Fi and hotspots—it still doesn’t ensure complete network security.
What Are The Problems With Traditional VPNs?
VPNs are outdated and no longer meet modern enterprises’ security needs and demands. Even though they encrypt data—they aren’t optimised for cloud-based applications and large-scale remote workplaces.
Here are the common problems with the traditional VPN security setup for your enterprise:
- Trusts everyone: VPNs enforce excessive implicit trust and trust all users—making it easier for malicious hackers to access and exploit your network.
- Difficult to scale: Since VPNs require significant operational expenditure and a lot of maintenance—they increase the management complexity and scalability difficulties.
- Increases attack surface: VPNs expose the IP addresses to the entire internet and only offers perimeter-based network security—allowing attackers to access network applications.
- Results in performance lag: VPNs lead to the backhauling of the user data traffic—resulting in latency, performance degradation, and network connectivity issues.
So, if not VPNs, then what? The answer is Zero Trust.
How Do Zero Trust Security Establishes Better Network Security Than VPN Tunnels?
The Zero Trust Security model is an ideal alternative to VPN connections. It works on the principle of “Never Trust, Always Verify” and restricts network access—providing access to only authorised and authenticated users and devices.
Compared to the VPN networking tunnel, the Zero Trust framework and architecture provide a unified and single-click secure access solution—ensuring better security, performance, and user experience.
Here are the advantages of Zero Trust Security over traditional VPNs.
- Strict authentication: Zero Trust Security authenticates and verifies each user and device before granting access to the network and its resources.
- Least privilege access: Unlike VPNs, Zero Trust doesn’t leave the network open once users enter it. Instead, its application-specific tunnels ensure that users or devices only access the applications they’re permitted to access to get their jobs done.
It also helps significantly reduce the attack surface and minimises online network attacks and cybersecurity threats.
- Enhanced user experience: It provides secure, seamless, and single-click access to all network applications hosted at any remote location—without backhauling or network latency issues.
- Offers much more simplicity: The Zero Trust Security model removes the redundant VPN-based security stacks—eliminating complex management issues and replacing them with a single unified, secure remote access solution.
- Ensures better privacy: It enforces a privacy-first approach—allowing you to ensure that your user traffic and data are only accessible to you and no one else on the internet.
Thus, compared to the traditional VPNs, Zero Trust offers much better security for your enterprise network.
Conclusion
While VPNs and VPN tunnels encrypt data and hide your IP address from the internet, their excessive implicit trust and management complexity make them less desirable for modern and large-scale workplace needs.
On the contrary, the Zero Trust model is a much better and more secure alternative to VPN that lets you leverage least privilege access and granular access controls and delivers seamless and high network performance and user experience.
So, if you wish to establish network security beyond VPN tunnels—we urge you to check out our InstaSafe VPN alternative, Zero Trust. We help you upgrade your security posture with a remote and cloud-ready Zero Trust model to enhance network security and user experience. So, check out our features or book a demo to learn more.
Key Products
MFA | I&AM | ZTNA | Zero Trust Application Access | Secure Enterprise Browser
Key Features
Single Sign On | Endpoint Security | Device Binding | Domain Joining | Always On VPN | Contextual Based Access | Clientless Remote Access | Device Posture Check
Key Solutions
VPN Alternatives | DevOps Security | Cloud Application Security | Secure Remote Access | VoIP Security
