Kaseya Ransomware Attack: What Companies Can Learn From It
In a world where every device is becoming smarter and more connected, security emerges as a major pain point, and one of the key considerations. And, the latest Kaseya Supply Chain Ransomware Attack was another grim confirmation of the same, after the recent WannaCry, Bad Rabbit, and NotPetya attacks.
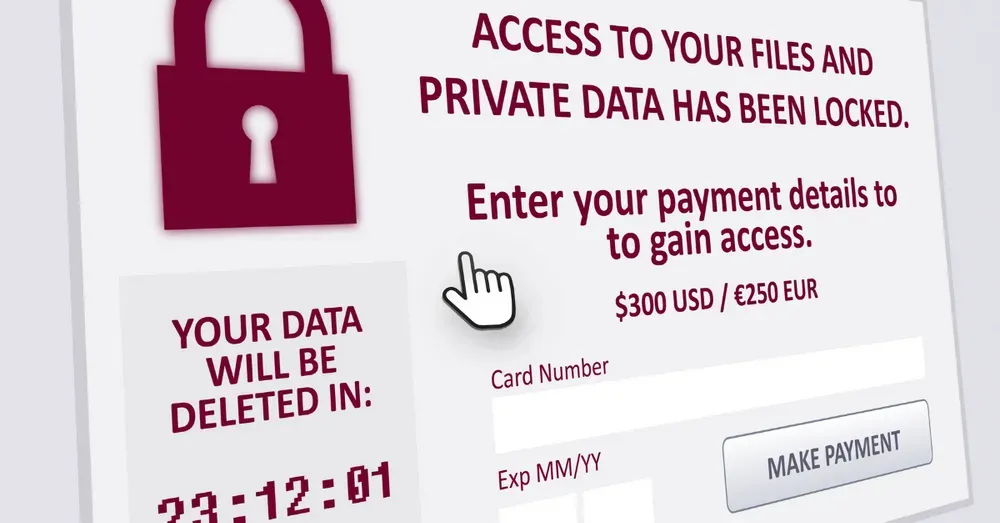
As per stats, every 14 seconds, a business falls victim to ransomware attacks, and it is highly likely that it might not even know about it is happening until the attacks have become threats and business risks!
While the security systems have certainly advanced from their versions a few years back, they have also become more vulnerable to hackers and attacks and failures, because of multiple reasons. Cloud servers, integrations, mobile apps, and web apps are some of the critical connection points in the network of an organization. And, if these points or nodes are not managed, monitored, and secured properly, it can cause unimaginable ramifications.
Here, we explore the background story of Kaseya’s Ransomware episode and draw inferences from the same to figure out how companies can learn from it.
Let us begin with a small recapturing of the entire incident.
Kaseya Ransomeware Attack – What, How, and Why?
On Friday, July 2, Kaseya’s backend infrastructure was attacked by a ransomware gang, and abused by them to deploy a malicious update to VSA servers that were running on the client premises. This update installed the REvil ransomware from the VSA server to all the workstations that were connected to it. This way, all the other third-party networks of the other companies were impacted.
While another cybersecurity organization, DIVD, a Dutch company said that one of their team members had identified these zero-day vulnerabilities weeks before this attack. Then, the company reported these vulnerabilities to Kaseya via a responsible disclosure guideline document.
However, the attackers also figured out these vulnerabilities while Kaseya was in the process of fixing them, and infected the workstations of thousands of companies even before the Kaseya customers could install a security patch.
As Kaseya is an IT solutions provider for companies, that in turn provides managed services and other functionalities to third parties, by the time Kaseya could issue a notice, the ransomware was already running and blocking access to the files on thousands of computers.
How Could REvil Pass-on Without Being Noticed?
Earlier, Kaseya had advised its customers to exclude several folders from antivirus protection because of compatibility issues with the VSA server. While it facilitated automated updates, it left a tunnel for the attackers into the customers’ computers, once they have compromised the VSA server.
Thus, REvil benefited in more than one way, such as:
- The initial compromise was done via a trusted channel
- Easy access was available to the customers’ systems because of anti-virus bypass
- Kaseya requires set-up for working folders and anything that was monitored by Kaseya Agent Monitor was obviously ignored and excluded from speculation.
Another powerful factor for the attack to spread enormously was the fact that the REvil actors didn’t attempt to delete the volume shadow copies and didn’t exfiltrate any data from the victim computers. This way, it was able to bypass the anti malware products and threat detection modules.
Finally, on July 5, Kaseya reported that the fix has been developed and will be initially deployed to SaaS environments, after the testing and validation checks.
Kaseya Ransomware Attack: Red Flags Raised
This is not the first time a major organization has fallen prey to ransomware attacks, or security threats. And, we agree that expecting that nothing of the sort will ever happen again, is nothing more than a Utopia.
However, this fiasco definitely raised some red flags, for the vendors, as well as the customers.
Below, we explore them one by one!
How trustworthy is a leading security or IT solutions provider?
Trust is an intangible asset that has a direct impact on the business operations and the way the entire IT community works, especially when it comes to the third-party provider.
Kaseya is a leading IT solutions provider and has a clientele to boast of. With an extremely talented and agile team at work, the company still couldn’t ward off the attacks.
This puts all the companies under scanner and businesses leveraging third-party services have also become warier.
While we cannot simply stop trusting the brands and businesses, it is the duty of both, the vendor and the user to ensure that a consistent and regular check is conducted for ensuring maximum security.
Why are external reviews and monitoring important?
When you have an ample number of in-house resources, the companies tend to forget one thing – all of them have a singular view of their products and services. The team members are not going to think and act like an attacker, and even if they manage to do so for some time, they cannot ensure that things stay the same always!
This is why, the external audits, tests, and monitoring of products and services are important.
Well, this is easily said than done; right?
Because of the confidentiality, security breaches, and the entire business ethics thing, finding a way to do so is tough.
However, a few other things that companies can do include:
- Leveraging the alliances and hybrid organizations like ioXt to get other members on board with the reviews.
- Using the latest technologies like DAST etc for simulating the external attacks via software.
Help can come from unexpected places, and when it comes, you better be on your toes
Even before the attack happened, DIVD warned Kaseya about the impending doom, and that too weeks before the incident. While the team at Kaseya was working at its own pace to salvage the situation, there is no doubt that they should have put their best resources at work, to offer the solution as soon as possible.
Kaseya could also have used and leveraged the help from some external industry expert or hired new resources.
But, they keep working on the security patch, while forgetting one small thing – if DIVD could know there is something wrong with their server, anyone else with an intent to harm can certainly come to know about that.
Having a clear-cut strategy for such emergencies and critical times is a must!
Zero Trust Security
Finally, having a zero trust security policy is a must. If Kaseya customers had that in mind, they could have had a solution for compatibility issues without bypassing their antivirus programs.
Having a zero-trust security policy allows you to have a “Plan B or an additional layer” of security, just in case your vendor gets compromised.
Read More: InstaSafe is now a technology partner of Hewlett Packard Enterprise (HPE)
Wrapping it up
While nothing is permanently safe and impenetrable, building your digital fortress starts from Day 1. We recommend investing in the right security providers and developing fool-proof security and risk mitigation strategies right from the start.
Also, keep revisiting them, modifying and updating them on a regular basis to ensure that vulnerabilities are identified and resolved well before they turn into threats!
Biometric Based Authentication | Certificate Based Authentication in Network Security | Device Binding Meaning | Posture Check Device | What is Always on VPN | FIDO Security | What Is FIDO2 | LDAP SSO Integration | What is Multi Factor Authentication | What is Passwordless Authentication | What is Radius Authentication | SAML Full Form | SAML Single Sign ON | Software Defined Perimeter SDP | Devops Security Best Practices | What is Secure Remote Access | VPN Alternative for Business | VPN vs ZTNA | Zero Trust Model | ZTNA Architecture | Zero Trust Application
